Securing the Digital Frontier: How DNS Proxies Master Enterprise DDoS Protection
Does your enterprise truly stand resilient against the relentless wave of DDoS attacks targeting your core network services? In an era where digital presence dictates business continuity, the Domain Name System (DNS) remains a primary, often overlooked, vulnerability for sophisticated cyber threats. Protecting this critical infrastructure demands more than traditional defenses. It requires a strategic, architectural shift towards specialized solutions like the DNS proxy.
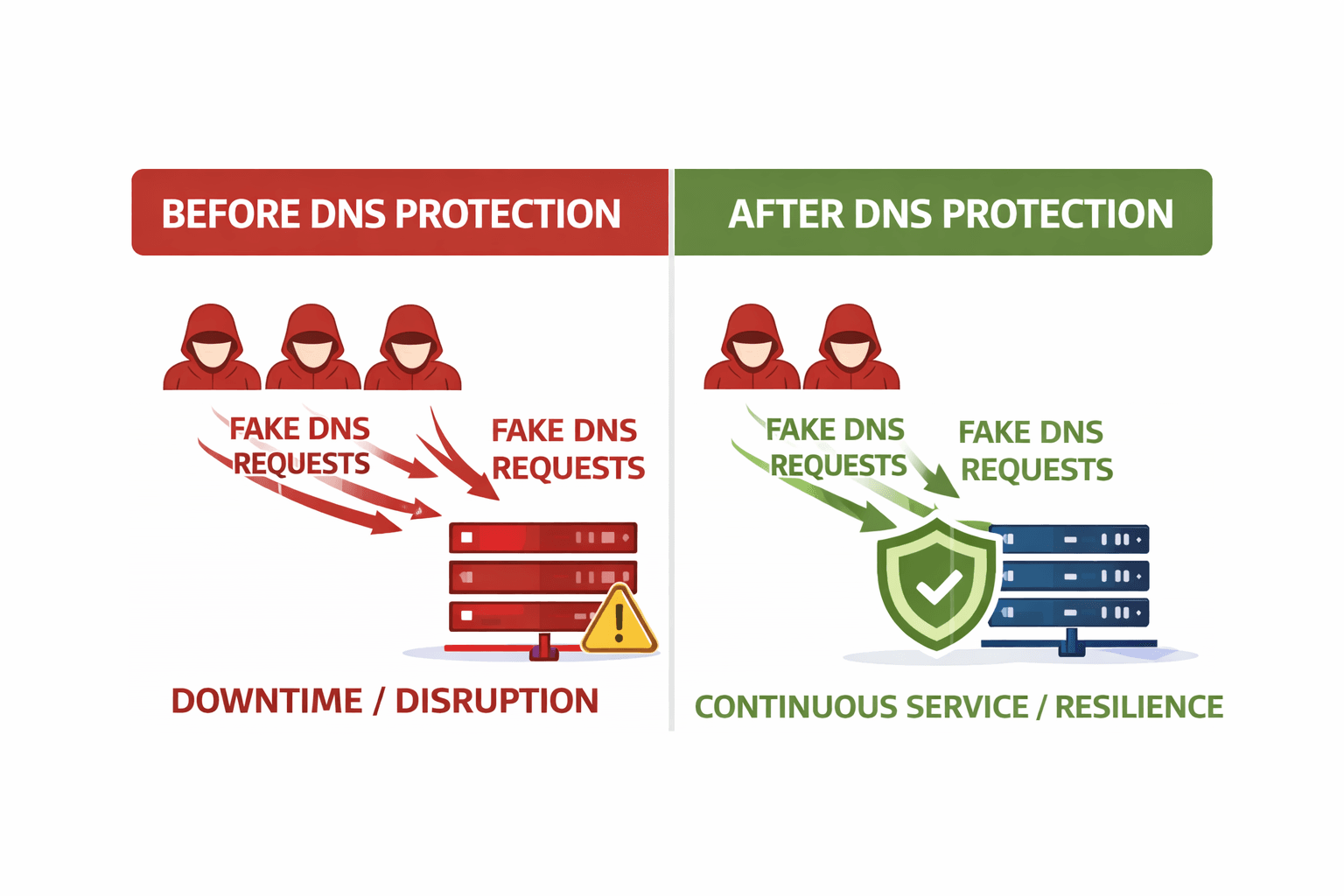
Direct Answer Box: Yes, a DNS proxy significantly enhances enterprise DDoS protection by acting as an intelligent intermediary. It filters malicious traffic, caches legitimate queries, and routes requests to backend DNS servers, effectively shielding them from direct volumetric or reflective attacks, ensuring service continuity even under extreme duress.
Why Enterprise DNS Needs Protection
Enterprise DNS infrastructure forms the bedrock of all network communications. It translates human-readable domain names into machine-readable IP addresses. Any disruption to this service immediately cripples access to websites, applications, and critical internal systems.
DDoS attacks against DNS are not merely an inconvenience; they are direct assaults on business operations. A successful attack can lead to widespread outages, significant financial losses, reputational damage, and potential compliance breaches under regulations like GDPR or ISO 27001. Protecting this layer is paramount for maintaining uninterrupted digital services.
How DNS Proxies Stop DDoS
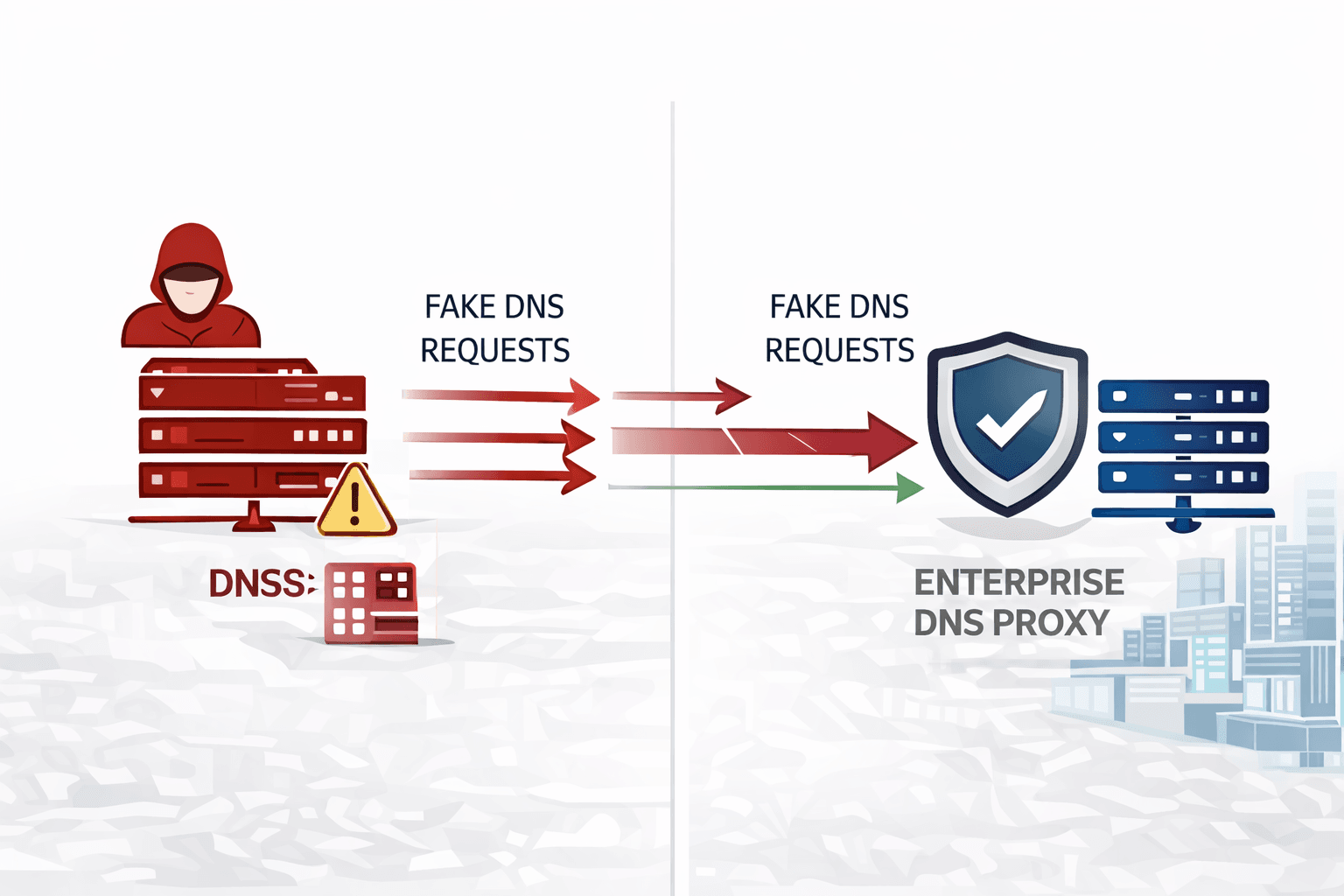
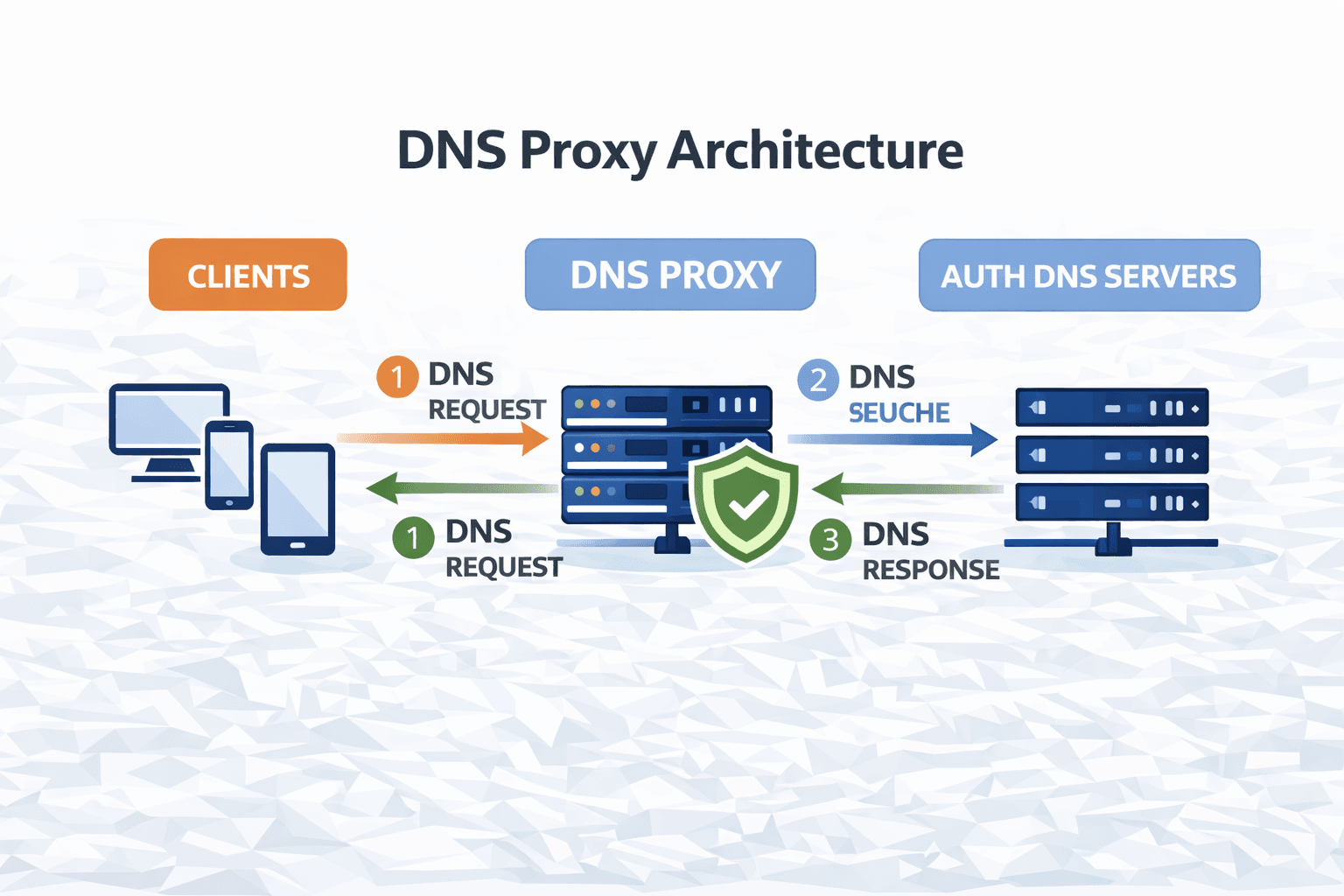
A DNS proxy acts as a sophisticated, intelligent intermediary between clients and authoritative DNS servers. Its core architecture involves intercepting all DNS traffic, inspecting it for malicious patterns, and forwarding only legitimate queries to the backend. This strategic positioning provides a robust first line of defense.
How DNS Proxy Works (Step-by-Step)
1. User sends DNS request
2. DNS proxy intercepts request
3. Malicious traffic filtered
4. Clean request forwarded
5. Response returned to user
The proxy employs multiple mitigation techniques. Rate limiting prevents volumetric attacks by capping the number of queries from a single source or subnet. Anomaly detection identifies unusual query patterns or sudden spikes that indicate an attack. Furthermore, IP reputation databases block known malicious sources before they can reach the enterprise's internal DNS.
This layered approach offloads the burden from backend servers, allowing them to focus solely on serving valid requests. The proxy effectively absorbs and neutralizes the attack traffic, preserving the availability of critical DNS services. This is central to effective dnsproxy enterprise ddos protection.
Common Enterprise Attack Vectors
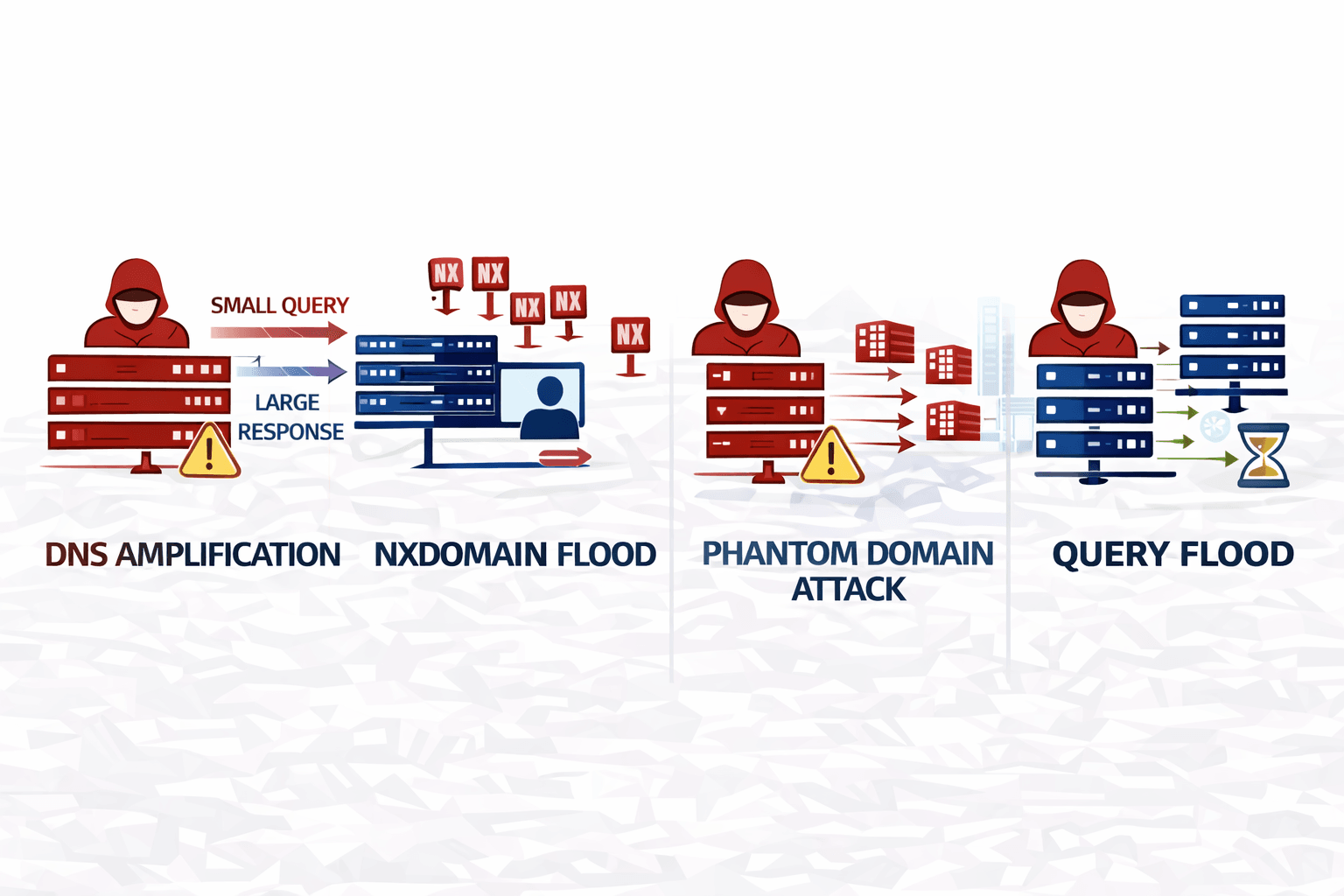
Enterprise DNS faces a diverse array of DDoS attack vectors, each designed to exploit different vulnerabilities. Understanding these specific threats is crucial for designing effective defenses. Attackers constantly evolve their methods, targeting the enterprise's most vital services.
Common attacks include:
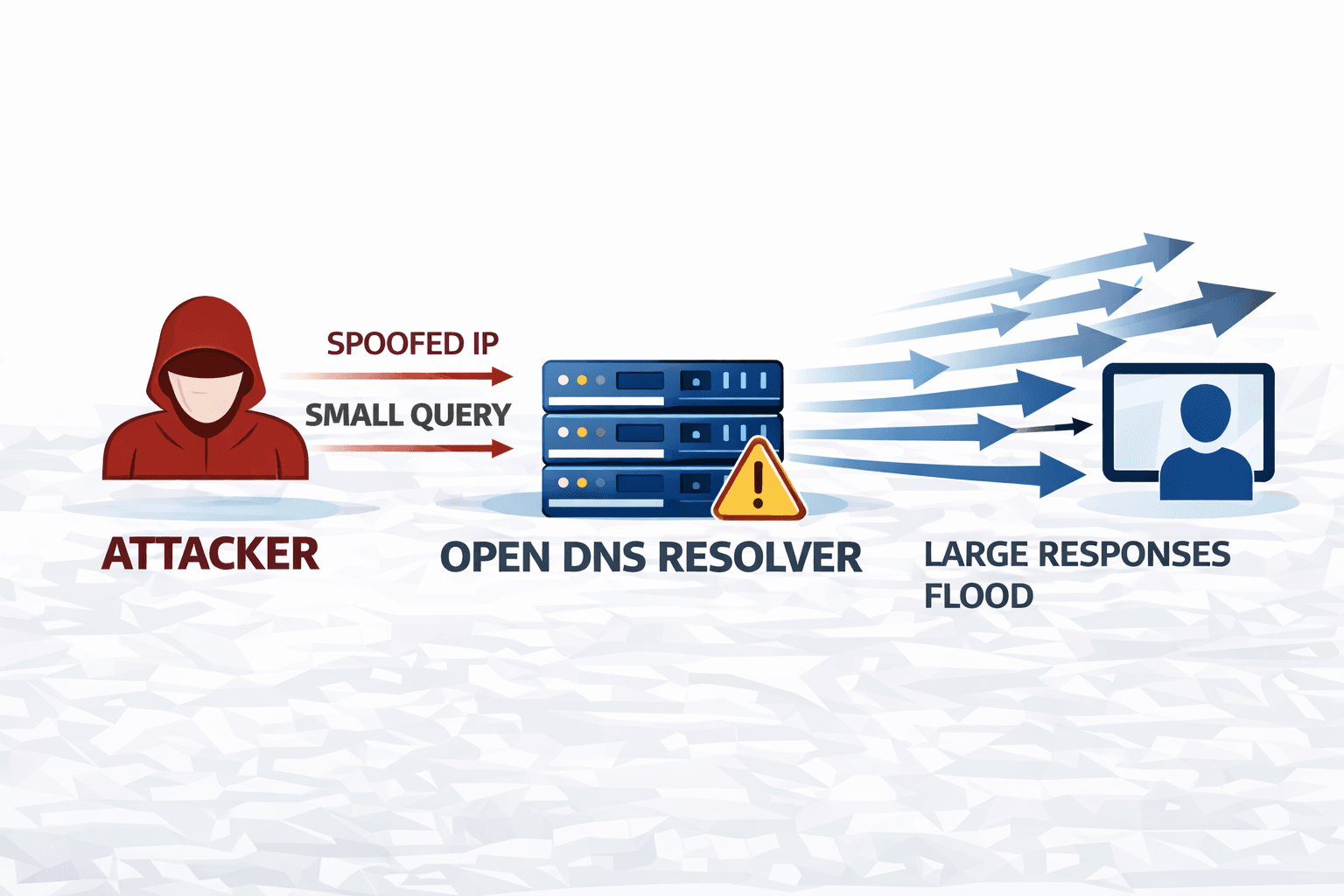
- DNS Amplification/Reflection: Attackers spoof the victim's IP address and send small queries to open DNS resolvers. These resolvers then flood the victim with large responses, amplifying the attack volume.
- NXDOMAIN Floods: Malicious actors bombard the DNS server with requests for non-existent domains. This forces the server to expend resources searching for records that do not exist, leading to resource exhaustion.
- Phantom Domain Attacks: Similar to NXDOMAIN, but attackers target a few specific, non-existent domains repeatedly. This can overwhelm caching mechanisms and backend server processes.
- DNS Query Floods: A high volume of legitimate-looking DNS queries overwhelms the server, consuming its processing power and bandwidth. This is often harder to detect than other attacks.
Each of these vectors demands specific mitigation strategies that a well-architected DNS proxy can provide. Effective dnsproxy enterprise ddos protection directly counters these persistent threats.
Building Multi-Layered Defense
A single solution rarely provides comprehensive security. True enterprise resilience against DDoS attacks demands a defense-in-depth strategy, integrating a DNS proxy with other security controls. This multi-layered approach creates a formidable barrier, making it significantly harder for attackers to penetrate.
Integrating the DNS proxy with Web Application Firewalls (WAFs) protects web-facing applications from Layer 7 attacks, while traditional firewalls handle network-level filtering. Threat intelligence feeds provide real-time updates on known malicious IPs and attack patterns, enhancing the proxy's filtering capabilities.
Professional Scenario: During a recent compliance audit for a financial services firm, a simulated DNS amplification attack was launched. The firm's integrated DNS proxy, leveraging real-time threat intelligence and dynamic rate limiting, absorbed 98% of the malicious traffic, ensuring continuous service and demonstrating compliance with data availability clauses under CCPA.
This integrated approach ensures that even if one layer is bypassed, others remain active. It reinforces the enterprise's security posture, meeting stringent regulatory requirements for data availability and integrity, such as those outlined in ISO 27001.
Ensuring Uptime: Scalability & High Availability
For enterprise-grade DDoS protection, the DNS proxy solution itself must be highly available and scalable. Any point of failure in the protection mechanism becomes a new vulnerability. Continuous uptime and consistent performance are non-negotiable requirements for critical infrastructure.
Scalability is achieved through distributed architectures and load balancing. Multiple DNS proxy instances can operate in parallel, handling increased query volumes without performance degradation. This allows the system to expand its capacity dynamically in response to attack surges.
High availability (HA) ensures that protection remains active even if a component fails. This involves redundant proxy servers, automatic failover mechanisms, and geographic distribution. Should one proxy instance go offline, traffic seamlessly redirects to another, preventing service interruptions. This robust design is fundamental to maintaining dnsproxy enterprise ddos protection during sustained attacks.
Choosing a DNS Proxy Solution
Selecting the right DNS proxy solution for enterprise DDoS protection requires careful consideration of several factors. Features, deployment model, and integration capabilities all play a crucial role in determining effectiveness. Enterprises must align the solution with their specific operational needs and existing security ecosystem.
Here is a comparison of key aspects to evaluate:
| Feature/Requirement | Cloud-Based DNS Proxy Service | On-Premise DNS Proxy Appliance |
|---|---|---|
| Deployment Model | Managed service, offloads infrastructure burden | Requires internal hardware/VMs, self-managed |
| Scalability | Inherently scalable, global network capacity | Scalability depends on hardware investment and architecture |
| Maintenance | Handled by vendor, automatic updates | Requires in-house IT team for updates, patches, and monitoring |
| Cost Structure | Subscription-based, operational expenditure (OpEx) | Capital expenditure (CapEx) for hardware, ongoing OpEx |
| Control & Customization | Limited to vendor-provided options | Full control over configuration, deeper integration possible |
| Threat Intelligence | Often leverages vast, real-time global threat feeds | Relies on integrated feeds or manual updates |
| Latency Impact | Potentially higher for geographically distant users | Lower latency for local users |
| Compliance | Vendor must meet enterprise compliance needs | Enterprise responsible for all compliance aspects |
Enterprises must weigh the benefits of a managed service's ease of use and inherent scalability against the granular control and potential lower latency of an on-premise deployment. The choice significantly impacts the long-term effectiveness of dnsproxy enterprise ddos protection.
Final Thoughts
Enterprise DNS is not just infrastructure — it is a critical security layer.A DNS proxy ensures uptime, resilience, and protection against evolving DDoS threats.
Key Takeaways
- DNS proxy acts as first defense layer against DDoS
- Stops amplification, flood, and NXDOMAIN attacks
- Improves uptime and enterprise resilience
- Works best with multi-layered security strategy
Frequently Asked Questions
What is a DNS proxy?
A DNS proxy acts as an intermediary, forwarding DNS queries from clients to DNS servers. It can filter, cache, and modify requests, enhancing security and performance by shielding authoritative servers.
How does a DNS proxy differ from a traditional DNS server in DDoS protection?
A DNS proxy specifically focuses on security and traffic management before queries reach a traditional DNS server. A traditional server primarily resolves names; a proxy actively inspects and mitigates malicious traffic, acting as a protective shield.
Can a DNS proxy protect against all types of DDoS attacks?
No, a DNS proxy excels at mitigating DNS-specific DDoS attacks (e.g., amplification, floods) but typically requires integration with other security layers like WAFs and firewalls for comprehensive protection against all DDoS vectors.
What are the key considerations for deploying a DNS proxy in an enterprise environment?
Key considerations include scalability requirements, high availability, integration with existing security tools, management overhead, and compliance with regulatory standards.
Is a DNS proxy a standalone solution for DDoS, or part of a broader strategy?
A DNS proxy is most effective as a critical component within a broader, multi-layered defense-in-depth strategy, complementing other security measures like firewalls, WAFs, and threat intelligence platforms.



